
In 1983, the Apple Lisa Computer appeared: the first home computer with a GUI, graphical user interface, and the lowering of the cost of personal computers led to great popularity in the home and business markets during the 1980s. In 1990, Tim Berners-Lee created the World Wide Web service on the Internet, and in 1995, August Microsoft released "32-bit" Windows95, amid incredible hype.
From its inception in 1975, the PC has in the modern day become a focal point of business, education, and home life. It has emerged as the second most significant media device after television, and the average American spends about 2 hours everyday behind the computer. Of all children, 69 per cent have a computer at home, and 45 per cent have Internet access at home.
Computers are such common place now, and are used so often by children, that they can be intrusive in the home and on the family, and can have a negative influence on them in a variety of ways. Parents often hope that the computer will be used for positive reasons; for education and assistance with homework, but unfortunately more often than not often it is used for playing games, surfing the Internet, chatting with friends or strangers, and watching films. The following diagram gives a breakdown of how the computer is used by children. As it can been seen, only 22% of computer time is used in order to do homework.
Unlike in 1975, when a PC's use was very limited, modern day computers have so many functions now that parents can no longer sit back and give free reign over the computer to their children. Parents need to restrict its use in some way, so as it can a source of benefit to their children, and not a source of harm.
Chronager, a new program by the highly acclaimed Internet filtering software company SoftForYou' has been designed to give parents total control over how and when their children can use the home computer. The program's beauty lies in its simplicity of use, and in its power that it gives to parents to control how and when the computer is used by each individual member of the family.
A description of the functions of Chronager will follow, and an explanation of their use and importance.
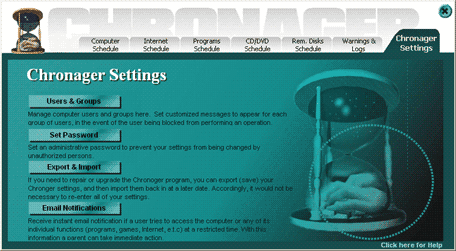
When you enter into the Chronager program, the main page is laid out as follows:
It may be acceptable to parents for an older teenager to spend more time surfing the Internet, or playing games, and to have access to the computer as a whole later at night. However, for a younger child, parents may want the main function of the computer to be an educational one. i.e. to do homework. In this case a different set of restrictions would be required. Access to the computer during early evening only, for instance, and less access granted to watching movies and playing games.
By clicking on Computer users, you enter the page where you can register individual users. Simply by typing in the name of each child, parents are then able to subsequently set each level of restriction tailored specifically to each child.

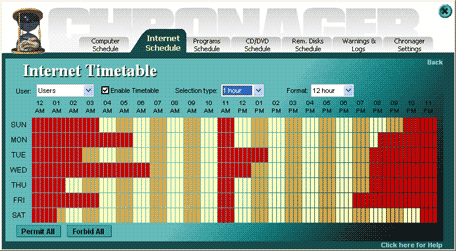
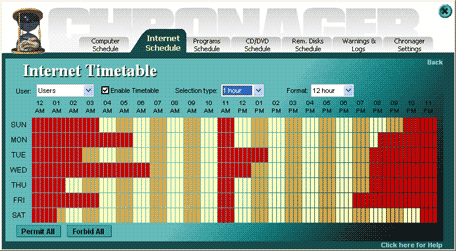
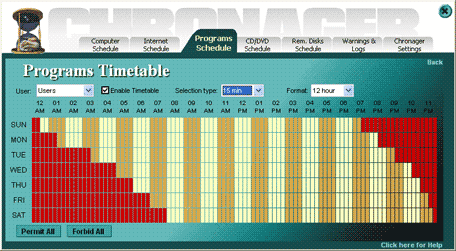
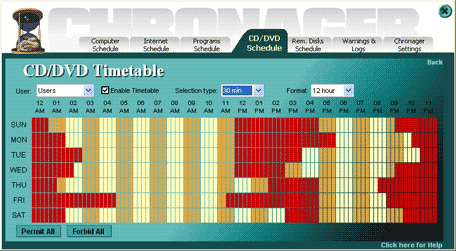
Each operation is limited by simply marking on a timetable which times access is to be allowed, and which times it is to be restricted. The time table is clearly laid out, and easy to use. It is depicted as follows:
Chronager enables you to control and restrict the activity of 5 operations, as listed in Schedule manager:
1) Computer activity
2) Internet
3) Programs
4) CD/DVD ROMs
5) Removable disks
1) Computer Activity Schedule (when the computer can be switched on and used as a whole)
With the capability of modern day computers to perform many different types of operation, and with the visual stimulation that they can provide to children, computers are places where children increasingly spend a considerable amount of their free time.
Unfortunately, unfettered access to the Internet can be very detrimental to the mental and even physical development of children. Time spend idly on chat sites, downloading music and playing games e.t.c. is more often than not of little educational value to a child, and if a lot of his or her free time is devoted to such activities, he or she is deprived of the necessary stimulus to develop mentally. This illusional world is no substitute for the real, and children are receiving stimulation in a very passive capacity, unlike the dynamic stimulus a child is exposed to in real life situations.
A child's creative abilities are more likely to develop fully when immersed in the real world, as apposed to this 2-dimensional world of fiction.
A child who spends too much time alone in this virtual world is likely to suffer a sense of alienation from other children and from people in general. It is very beneficial for children to spend leisure time with children of their own age, so as to develop the social skills required in adult life.
The virtual world can be a lonely one, and can cut children off from the necessary interaction with his or her peers. Physically, too much time behind the computer can also be harmful to children. Children lead a much more sedentary lifestyle than in previous generations, and in part this is due to computers. Child obesity is at an all time high. Too much time in front of a computer screen is also harmful to the development of eyesight. One of the possible problems that can arise due to intensive staring into the screen is sight deterioration. Hours of watching the monitor (mainly in darkened rooms) which displays rapidly changing pictures can impair sight, and if the player already had a weakened sight, it can only make the situation worse.
In Computer activity, you can control the amount of time a child spends on the computer, and therefore limit the harmful effects that are associated with spending too much time using it. Also, in the timetable, you can specify exactly when access to the computer will be allowed. This is very useful, as you can, for instance, restrict times of access to those when you can monitor the child; of particular importance if he or she is on the Internet and in chat rooms. It also means that parents can deny their child access to the computer after the child's bedtime, and allow access only when the child needs to do homework, or to a particular time allocated to entertainment.

2) Internet Schedule
Since its inception in 1995, the Internet has grown behind anyone's wildest dreams, and currently has an estimated 1 billion users worldwide. It can be a source of education for children, but unfortunately, this educational power of the Internet is tempered by the access that it allows children to endless sites containing undesirable articles, pictures and films.
These pages range from fairly mild to those of an extreme, violent and pedophiliac nature. Once found, such sites can expose a child to photos, videos and stories of a highly indecent and often shocking nature. The child is then able to freely download as many files as he/she likes and save them onto disk, thereby hiding from parents what has been viewed.
Chat sites are particularly common amongst children, as they offer previously unparalleled opportunities to communicate in real time with people from all corners of the globe.
However, not all of these people are benign. Many people use chat sites to seduce children and adolescents. In fact one in five children who use chat rooms have been approached over the Internet by pedophiles
With unlimited access, there are unlimited opportunities for a child to be exposed to web sites containing sexual imagery, violence, hostility, extremism and hate in a way that was impossible before the Internet came into common use, and therefore it is vital that parents control their child's use of the Internet.
3) Programs Schedule
Programs include, for instance, games, instant messaging and media players.
Modern day computer games can be very graphic and depict violence and sexual imagery. In these first years of the twenty-first century, computer-games have become one of the unavoidable elements of modern life of the young people.
Research shows that as many as 92% of children between 4 and 17 years of age play computer games.
The following list shows how popular different categories of games are;
Fantasy violence - 32%
Sport - 29%
General Entertainment - 20%
Human Violence - 17%
Educational Games - 2%
As can be seen violence is very common in modern day games. They are interactive and cast the player in the virtual world where they make the player identify himself with the main character whose actions have an influence on the plot. One of the greatest problems here is that murder and violence performed by the hero of the game are practically never punished, and often even rewarded. This creates a feeling in children that violence is right, and kids simply adopt violent behavior because they see nothing wrong about it.
Scientific research proved that children who played violent games tend to be more aggressive than the children who didn't.
Instant messaging is an Internet technology that lets you receive messages, files, and other data in real time. Whilst it is potentially useful, it can also be potentially dangerous. There are many reasons that parents need to be concerned about their child's use of this program. Some are listed below;
Private conversations can be started with anybody (including strangers) with many instant messaging programs.
Instant messaging provides the opportunity to release personal information in real time.
Instant messaging is also a place where online scams, identity theft, and other predatory behavior occur.
Instant messaging can be very addictive and time consuming and can get in the way of other activities.
Chronager enables parents to limit the use of such programs. Use of them could be completely constricted, or limited to so that children are able to have restricted access, for instance for an hour a day in the evening after they have done their homework.
4) CD/DVD ROM Schedule
The main use of the CD/DVD ROM for children is in order to install and play games and to watch movies. As described above, to much usage of such programs can be detrimental to their development. Chronager enables parents to limit the times when the CD/DVD ROM can be activated, and so protect children from the potential harmful effects of having unlimited access to CD/DVD's.
5) Removable disks
Another source of games, and also a convenient way to copy software between friends. Such software could potentially be infected with a virus. Henceforth it is desirable for parents to be able to restrict the use of the disk-drive. Again, Chronager puts full control of this computer operation into the hands of parents.

As a point of interest, current users of Chronager make use of the above described functions to a different degree. This degree corresponds to the order in which they were listed above;
1) Computer activity - The most popular and commonly used function.
2) Internet - The potential dangers that the Internet poses to children means that this is a vital and very popular function.
3) Programs - These can be from distracting to downright dangerous and so it is common for parents to restrict access to them.
4) CD/DVD ROMs and 5) Removable disks
As in Schedule manager, your ability to control the use of the computer not only applies to the computer as a whole, but to its individual operations; the Internet, programs and CD ROMs/removable disks.
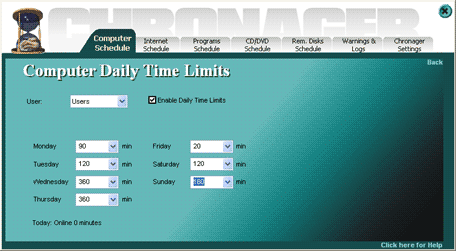
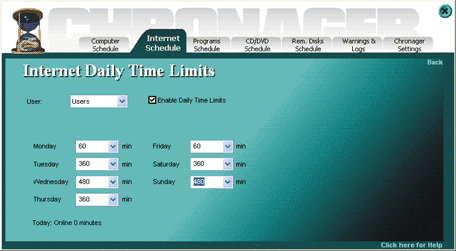
This function is useful if you desire to control how long your child spends on the computer and to what operations he or she has access to, but dont desire to restrict exactly when your child makes use of this permitted time. This may be, for instance, because your child is older, and you wish to give him or her more freedom and responsibility for their computer use. It is an especially useful function if your childs schedule is unpredictable or changes on a regular basis, and so it is impractical to schedule their use to particular times.
Computer activity schedule (when the computer can be switched on and used as a whole)
Too much time spent behind the computer can be detrimental to the mental and physical development of children. Hence it is of great benefit for parents to be able to control the amount of time their children spend on the computer.
Internet schedule
Children need to be protected from the many harmful aspects of the Internet, ranging from insatiable imagery to dangerous solicitation by predators. Limiting your childs use of the Internet is a must for concerned parents.
Programs schedule
Programs such as games, instant messaging and media players can be problematic for children for a variety of reasons, as were described above. With daily time limits you can take control of your childs use of such programs, and limit their use to a set amount of time per day.

CD/DVD ROMs and Removable disks
Limiting your childs use of this computer operation can be useful so that, for instance, your child doesnt have free reign to install and play any games that he or she wants.

With Daily time limits, you could, as an example, give your child daily access to the computer as a whole for 2 hours a day. Within those 2 hours you could then give him or her access to the Internet for 30 minutes to surf the web, to the CD/DVD ROM for 30 minutes to play games, and to the media player for 1 hour to watch films.
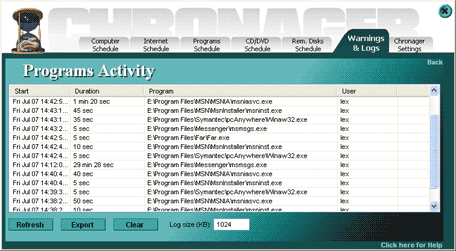
By clicking on Generated warnings, you enter the log of blocked operations which have been attempted to be accessed. This page is depicted as follows:

Any attempted violation of the established rules can be viewed, in an easy to use and clear format.
By clicking on Programs Activity, you will find a table of the same format, which lists which programs have been used during the period of computer activity. Hence you are able to discern whether games were played, music was listened to, or the Internet was accessed.
1) Administrator password: Here parents can set up an administrator password. This password is then required in order to enter into Chronager. All the settings are henceforth protected and only you will be able to change them.
2) Email notifications: This enables you to receive instant notification when a blocked operation is attempted to be accessed. This notification appears in your Email account, making it easier for you monitor any violations of the rules.
3) Export and Import settings: This enables you to save all of your settings, in the event of the need to re-install the software (if, for instance, you are updating the program to a newer one.)
Chronager is the perfect solution for parents concerned about the length of time and now the PC is been used by their children. Try the free 14-day trial version of Chronager and find out for yourself what benefit it can bring to your family.